


IPv6 configuration on a network interface

Static routes management

Cloud Provisioning workflow

Adding a Passkey in system settings

API Keys section in MikoPBX
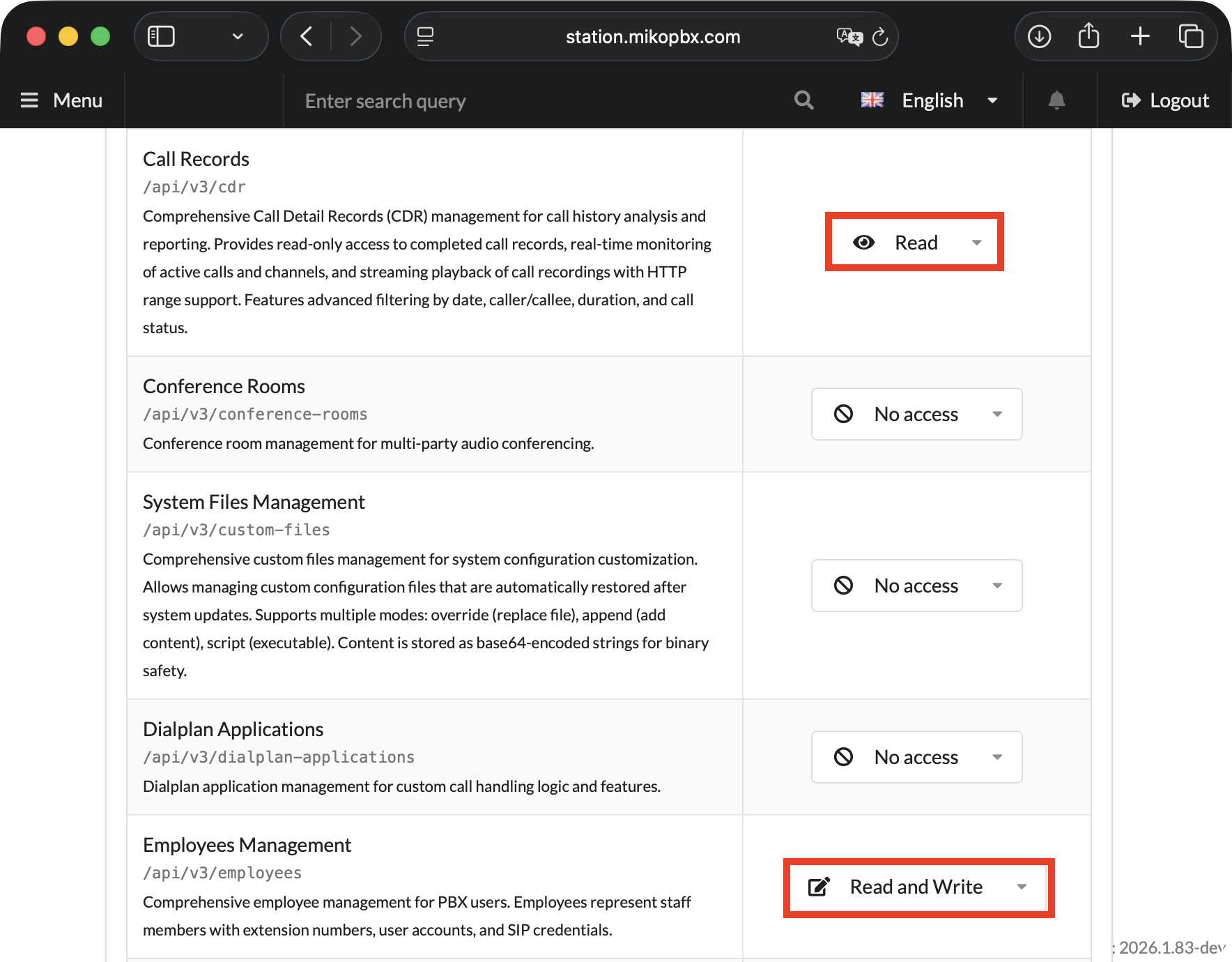
Example of granting Read access to Call Records and Read/Write to Employees Management

Country flags in the blocked IP list

S3 storage workflow diagram in MikoPBX

Enabling the ARI interface in the ARI Settings section

Adding an IAX trunk

Example OAuth2 configuration for Gmail

Example email notification on login

MikoPBX status menu

Employee import and result handling strategy

Interactive tooltips in provider settings

Disk space usage visualization

Intrusion protection level configuration

Blocked IP list